MalwareBazaar Database
You are currently viewing the MalwareBazaar entry for SHA256 cbe84e2c523fd51dabb1365df50415ffc51f8159c36798061742f08ba5d31b9b. While MalwareBazaar tries to identify whether the sample provided is malicious or not, there is no guarantee that a sample in MalwareBazaar is malicious.
Database Entry
Loki
Vendor detections: 11
| SHA256 hash: | cbe84e2c523fd51dabb1365df50415ffc51f8159c36798061742f08ba5d31b9b |
|---|---|
| SHA3-384 hash: | 7cebbe20a6c1982eb1485128e9eccd571e37c73df074b88ca7c471d0e60902aa1ca8b502ed9d604999e0cd3210c70550 |
| SHA1 hash: | 705c25adbdb7b805e47566540b3804eba178e7da |
| MD5 hash: | cf8b307caa943326ee808bb3cb02deee |
| humanhash: | two-jig-east-table |
| File name: | _2201S_BUSAN_HOCHIMINH_.xlsx |
| Download: | download sample |
| Signature | Loki |
| File size: | 191'736 bytes |
| First seen: | 2022-02-10 05:50:27 UTC |
| Last seen: | 2022-02-10 14:25:59 UTC |
| File type: | |
| MIME type: | application/encrypted |
| ssdeep | 3072:W3x5yiKm7/AJj6GEOux8NBVuVnDcq3QT0PyYC9v1EFVW3NdR31od+xXfwsRYXn0D:uam7/AJ6GsWBVuV4MaB9voVWdT3iWPws |
| TLSH | T1DB14126E72932523F1A212321102436A9D79FD5A7E379178A6387FCC9EBF5C925B0E40 |
| Reporter | |
| Tags: | CVE-2017-11882 Loki VelvetSweatshop xlsx |
Office OLE Information
This malware samples appears to be an Office document. The following table provides more information about this document using oletools and oledump.
OLE dump
| Detection: VelvetSweatshop |
MalwareBazaar was able to identify 6 sections in this file using oledump:
| Section ID | Section size | Section name |
|---|---|---|
| 1 | 64 bytes | DataSpaces/DataSpaceInfo/StrongEncryptionDataSpace |
| 2 | 112 bytes | DataSpaces/DataSpaceMap |
| 3 | 208 bytes | DataSpaces/TransformInfo/StrongEncryptionTransform/Primary |
| 4 | 76 bytes | DataSpaces/Version |
| 5 | 185080 bytes | EncryptedPackage |
| 6 | 224 bytes | EncryptionInfo |
Intelligence
File Origin
# of uploads :
5
# of downloads :
129
Origin country :
n/a
Vendor Threat Intelligence
Detection(s):
Result
Verdict:
Malware
Maliciousness:
Behaviour
Searching for the window
DNS request
Creating a window
Searching for synchronization primitives
Launching a process
Creating a file
Сreating synchronization primitives
Sending a custom TCP request
Creating a file in the %temp% directory
Reading critical registry keys
Changing a file
Creating a file in the %AppData% subdirectories
Moving a file to the %AppData% subdirectory
Enabling the 'hidden' option for recently created files
Unauthorized injection to a recently created process by context flags manipulation
Stealing user critical data
Query of malicious DNS domain
Sending an HTTP GET request to an infection source by exploiting the app vulnerability
Creating a process from a recently created file
Sending an HTTP POST request to an infection source
Result
Verdict:
Malicious
File Type:
OOXML Excel File with Embedding Objects in Encrypted Excel File
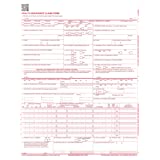
Document image
Image:
Verdict:
Malicious
Threat level:
10/10
Confidence:
100%
Tags:
control.exe embedequation exploit shell32.dll shellcode VelvetSweatshop
Label:
Malicious
Suspicious Score:
9.8/10
Score Malicious:
99%
Score Benign:
1%
Result
Verdict:
MALICIOUS
Link:
Details
Macro Execution Coercion
Detected a document that appears to social engineer the user into activating embedded logic.
Document With No Content
Document contains little or no semantic information.
Result
Threat name:
Lokibot
Detection:
malicious
Classification:
troj.spyw.expl.evad
Score:
100 / 100
Signature
Antivirus detection for URL or domain
C2 URLs / IPs found in malware configuration
Drops PE files to the user root directory
Found evasive API chain (may stop execution after reading information in the PEB, e.g. number of processors)
Found malware configuration
Injects a PE file into a foreign processes
Machine Learning detection for dropped file
Malicious sample detected (through community Yara rule)
Multi AV Scanner detection for domain / URL
Multi AV Scanner detection for dropped file
Multi AV Scanner detection for submitted file
Office equation editor drops PE file
Office equation editor starts processes (likely CVE 2017-11882 or CVE-2018-0802)
Sigma detected: Droppers Exploiting CVE-2017-11882
Sigma detected: EQNEDT32.EXE connecting to internet
Sigma detected: Execution from Suspicious Folder
Sigma detected: File Dropped By EQNEDT32EXE
Snort IDS alert for network traffic (e.g. based on Emerging Threat rules)
Tries to harvest and steal browser information (history, passwords, etc)
Tries to harvest and steal ftp login credentials
Tries to harvest and steal Putty / WinSCP information (sessions, passwords, etc)
Tries to steal Mail credentials (via file / registry access)
Tries to steal Mail credentials (via file registry)
Yara detected aPLib compressed binary
Yara detected Lokibot
Behaviour
Behavior Graph:
Threat name:
Document-Office.Exploit.CVE-2017-11882
Status:
Malicious
First seen:
2022-02-10 02:54:10 UTC
File Type:
Document
Extracted files:
51
AV detection:
18 of 42 (42.86%)
Threat level:
5/5
Detection(s):
Suspicious file
Result
Malware family:
lokibot
Score:
10/10
Tags:
family:lokibot collection spyware stealer trojan
Behaviour
Checks processor information in registry
Enumerates system info in registry
Launches Equation Editor
Modifies Internet Explorer settings
Modifies data under HKEY_USERS
Modifies registry class
Suspicious behavior: AddClipboardFormatListener
Suspicious use of AdjustPrivilegeToken
Suspicious use of SetWindowsHookEx
Suspicious use of WriteProcessMemory
outlook_office_path
outlook_win_path
NSIS installer
Enumerates physical storage devices
Drops file in Windows directory
Suspicious use of SetThreadContext
Accesses Microsoft Outlook profiles
Loads dropped DLL
Reads user/profile data of web browsers
Uses the VBS compiler for execution
Blocklisted process makes network request
Downloads MZ/PE file
Executes dropped EXE
Lokibot
Malware Config
C2 Extraction:
http://asiaoil.bar//bobby/five/fre.php
http://kbfvzoboss.bid/alien/fre.php
http://alphastand.trade/alien/fre.php
http://alphastand.win/alien/fre.php
http://alphastand.top/alien/fre.php
http://kbfvzoboss.bid/alien/fre.php
http://alphastand.trade/alien/fre.php
http://alphastand.win/alien/fre.php
http://alphastand.top/alien/fre.php
Malware family:
Lokibot
Verdict:
Malicious
Please note that we are no longer able to provide a coverage score for Virus Total.
File information
The table below shows additional information about this malware sample such as delivery method and external references.
Malspam
Delivery method
Distributed via e-mail attachment
Comments
Login required
You need to login to in order to write a comment. Login with your abuse.ch account.